ONSITE • REMOTE • CLOUD
What Is DFIR?
Whatever the cyber incident is (malware, data leakage, exfiltration, tampering of data, phishing, scams, loss of backups, ransomware, insider threats, or any other), our expert staff will analyze the case and draw up conclusions and recommendations to improve resilience.
Legal, Business and Commercial departments do not always know how to proceed. Shall we pay the ransomware note? Do we have to report the facts to the police? Do we have the necessary expertise and resources in house to conduct a rigorous forensics investigation?
One eSecurity Digital Forensics Service will allow our clients to answer questions about a cyber incident, such as:
- What happened?
- How was it possible?
- When did it happen?
- Who did it?
- Why did it happened?
One eSecurity advises and assists the different departments and, especially, the various managers involved in incidents.
Not all forensics cases have the same treatment, each type requires a different approach. That is why One eSecurity treats each case according to its type, adapting its processes depending on whether the cases are going to be administrative, civil or criminal, and always using the best practices in the digital forensics field.
| DIGITAL FORENSICS AND INCIDENT RESPONSE (DFIR) SERVICES | |
|---|---|
| What objectives do we pursue? | When? |
| * Identify and gather evidence of computer malicious activity in a forensically sound manner. * Ensure in depth-analysis of digital evidence. * Get to know what happened within your systems and what was the root cause of an incident. * Identify external malicious actors and possible insiders in your organization. * Support prosecution of the perpetrator of an incident. * Help protect the organization against future similar incidents. * Evaluate, maintain, and improve existing DFIR capabilities of your teams. * Help prepare for incidents in advance, ensuring integrity and continuity of the IT infrastructure. | * During and after an incident, to gain an in-depth knowledge of the activity occurred. * As a resilient strategy to prepare for cybersecurity incidents. * In order to respond to and resolve investigative hypothesis. * For securing and strengthening defense mechanisms as well as closing security gaps. * To ensure prosecution legal compliance. * In order to counter-expertise an existing digital forensics process or report. * To settle disputes among employees or between the employer and employees, based on digital evidence. * When aiming to increase to improve forensic readiness capabilities, based on forensic processes and procedures. |
DFIR Phases
The service is made up of the following phases based on NIST standards:
| Phase | Description |
| Acquisition | Identifying, labeling, recording, and acquiring data from possible sources of relevant data, following procedures that preserve the integrity of the data. One eSecurity is able to provide the technological means to collect large volumes of evidence while preserving the chain of custody. |
| Processing | Triage, processing and correlation of collected data using a combination of tools, automated and manual methods and techniques, assessing and extracting data of particular interest for the investigation and being able to deliver comprehensive forensic outputs to multidisciplinary investigation teams. |
| Analysis | Analyzing forensics output of the previous phase, to achieve the objectives of the investigation, considering a series of plausible hypotheses to obtain the answers that prove or refute evidential indicators. This analysis is performed by a group of analysts made up of experts in digital forensics, along with other disciplines, and supported by a state-of-the-art proprietary technology. |
| Report | Reporting the results of the analysis as well as detailing the methodology used throughout the investigation. One eSecurity adjusts the reporting level to the needs of the target, addressing technical and/or executive audiences, as well as expert reports for legal proceedings. In all cases, reporting determines what digital evidence supports what hypothesis and what conclusions can be drawn from the investigation process. |
What One eSecurity Offers Over Our Competitors
Experience
Our Digital Forensics service is formed by experts from the Emergency Incident Response, Cyber Threat Intelligence, and Threat Hunting departments that analyze and investigate any evidence of malicious activity. All our knowledge and experience adds to this service in order to find and identify any threat.
Swiftness
Thanks to One eSecurity's versatile and experienced DFIR team we are able to gather and process a great number of evidence in a very short time.
Flexibility
Our team can be activated when and for whatever you need. Our different service modalities allow our clients to get the coverage needed: on demand, as a retainer, locally or remotely. Our team is available and ready to work anywhere in the world.
Integration
Emergency Incident Response is not an isolated activity that is added to your organization. One eSecurity will make sure processes are integrated with the client's existing processes and infrastructure.
Software and Hardware
One eSecurity works with carefully selected industry leading strategic security vendors, in order to provide the best-of-breed digital forensic solutions. Each case is different and needs a different approach, while tools also differ depending on the platform, operating system, and the type of the target device. One eSecurity uses hardware and software tools, commercial and open source, chosen according to design, specific purpose or broader functionality.
SKY
During the more than 10 years delivering DFIR services, both as Incident Respondents and Forensic Analysts in many environments, reviewing thousands of systems, we have been progressively developing our own DFIR analysis system, known as SKY.
The SKY platform has been designed not only to automate most of the usual orchestration work, needed to manage DF/IR cases, but also to be an automated investigation and analysis system that is able to process evidence (live or already acquired systems), with the specific tools needed, and to integrate the results in a centralized analysis environment.
SKY’s modular design has been created to make it possible to handle different kinds of cases and process multiple types of evidence found in the victim's systems, such as media, memory or network traffic.
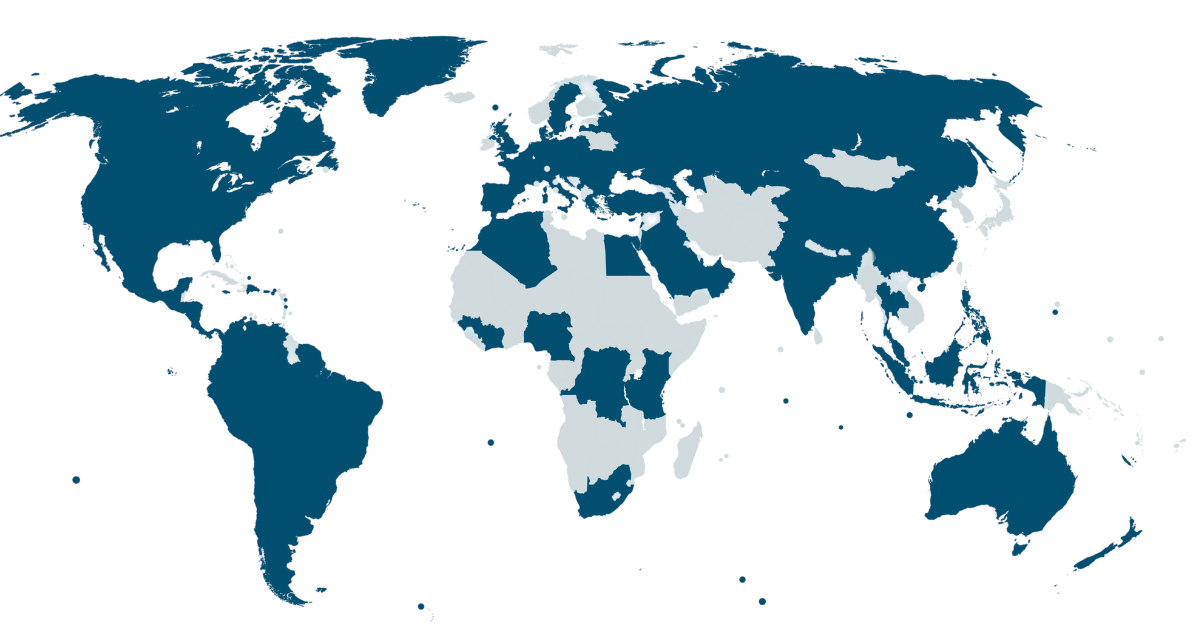
Explore the global reach of our DFIR operations. This map highlights the countries where we have successfully conducted Digital Forensics and Incident Response activities, helping organizations mitigate and recover from cyber threats.
Related To Our Services
| Emergency Incident Response | Threat Hunting Service | Cyber Threat Intelligence |
|---|---|---|
| One eSecurity Emergency Incident Response is aimed at clients who need agile response and support when a security incident happens. | Our Threat Hunting service combines the analytic capacity of our most experienced experts with the power and automation of our Hunting Framework, offering a continuous and proactive threat search process in both networks and systems. | The Cyber Threat Intelligence service by One eSecurity provides (both internally and for clients) knowledge and information on key threats for decision-making and forecasts of risk situations on IT systems and networks. |
| Learn more | Learn more | Learn more |
